Cybersecurity Audit in Embedded Systems: Testing and Risk Mitigating
Project in a Nutshell: Promwad performed a cybersecurity audit for a manufacturer of industrial equipment, assessing the security of their Microchip VSC7558-based system. We analysed hardware, software, cryptographic subsystems, and external interfaces to identify vulnerabilities. Using the MITRE EMB3D™ Threat Model, we mapped attack surfaces and verified compliance with IEC 62443-4-2, FIPS 140, and GDPR. The scope included SBOM analysis, cryptographic evaluation, and penetration testing. Based on the findings, we proposed targeted improvements to reduce cyber risks and support certification readiness.
Client & Challenge
Our client develops industrial equipment and aims to ensure its compliance with international security standards. To achieve this, a comprehensive assessment of the device’s hardware and software was required to identify potential vulnerabilities and evaluate cybersecurity risks.
The client asked Promwad to perform a security audit of the Microchip VSC7558 board for compliance with the following standards and threat models:
- MITRE EMB3D™ Threat Model: a framework for identifying cyber threats in embedded systems.
- IEC 62443-4-2: cybersecurity standard for industrial automation systems.
- FIPS 140: US government standard for cryptographic security in hardware and software.
- GDPR: European regulation governing data protection and privacy.
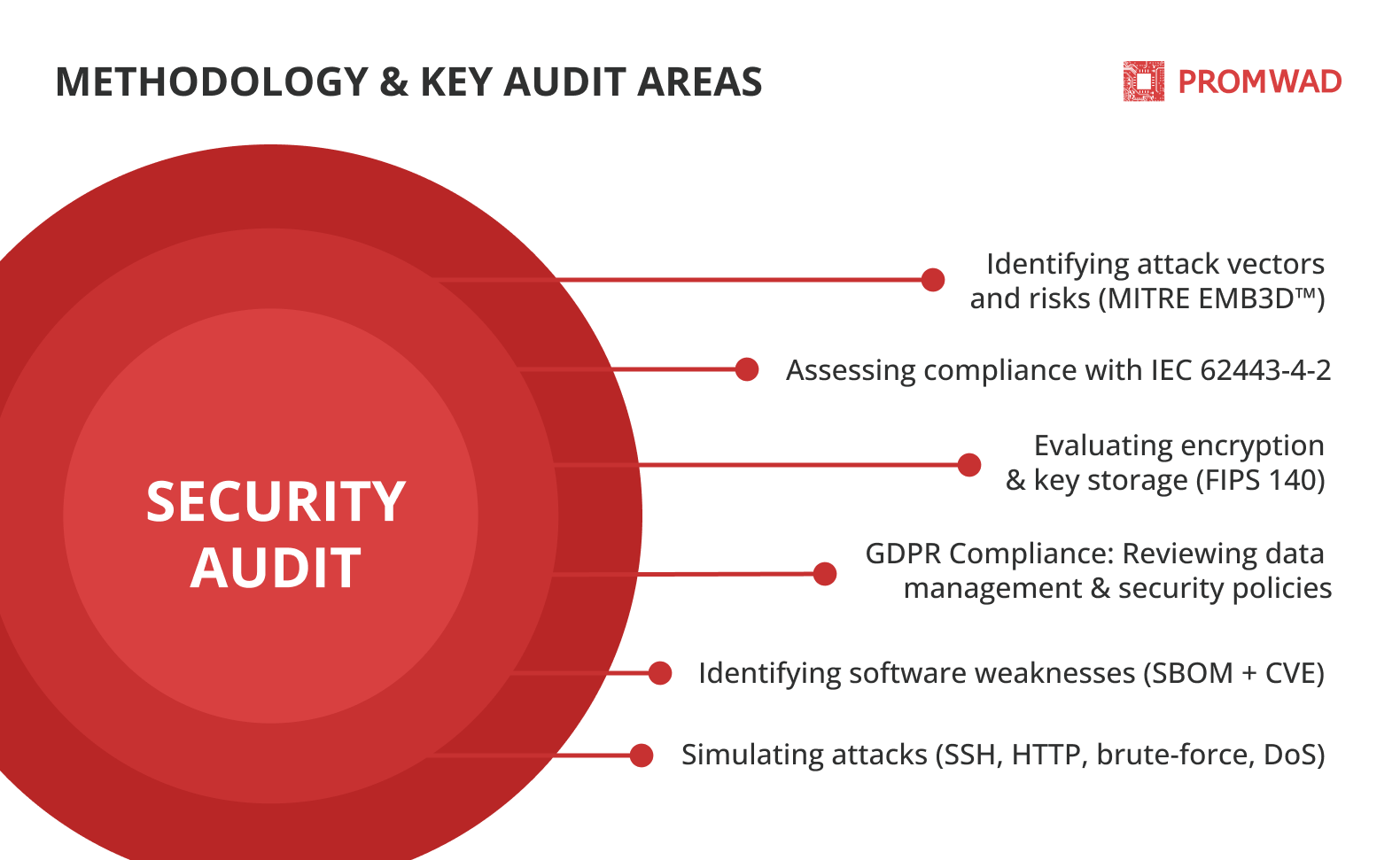
Methodology & Key Audit Areas
During the audit, we assessed the evaluation of hardware and software components, identified vulnerabilities, and tested the system's resistance to attack. The audit covered the following areas:
- Threat modelling and risk assessment: identified potential attack vectors and security risks based on the MITRE EMB3D™ Threat Model.
- Compliance analysis against IEC 62443-4-2: created a compliance matrix, identified deviations, and provided mitigation strategies.
- Cryptographic security evaluation (FIPS 140): assessed the strength of encryption algorithms and the security of key storage mechanisms.
- GDPR compliance audit: reviewed user data management practices, data storage security, and update policies.
- Software components and vulnerability analysis (SBOM + CVE): compiled a list of software components, identified security vulnerabilities and assessed third-party dependencies.
- Penetration testing: simulated attacks on SSH, HTTP, brute-force, and DoS to evaluate system resilience and identify potential security gaps.
Audit Results
The security audit identified several critical vulnerabilities that could compromise the device’s security and compliance. The key findings are:
Firmware and System Integrity (MITRE EMB3D™ Threat Model & IEC 62443-4-2)
- No Secure Boot, allowing unauthorised or modified firmware to be loaded.
- Open hardware interfaces (JTAG, UART), enabling low-level system access.
- Potential for executing unauthorised code, increasing the risk of system exploitation.
Cryptographic Security (FIPS 140)
- The embedded TLS library does not comply with security standards.
- No secure key storage, making encryption keys vulnerable to extraction.
Data Protection and Compliance (GDPR)
- Weak password policies make brute-force attacks more effective.
- No secure update mechanism, exposing the device to security risks from outdated software.
- Lack of a structured vulnerability management policy, preventing timely security patches.
Penetration Testing Findings
- Brute-force attacks on SSH successfully bypassed authentication due to weak credentials.
- Dictionary-based attacks exploited the lack of password complexity enforcement.
- Denial-of-Service (DoS) attacks disrupted device functionality.
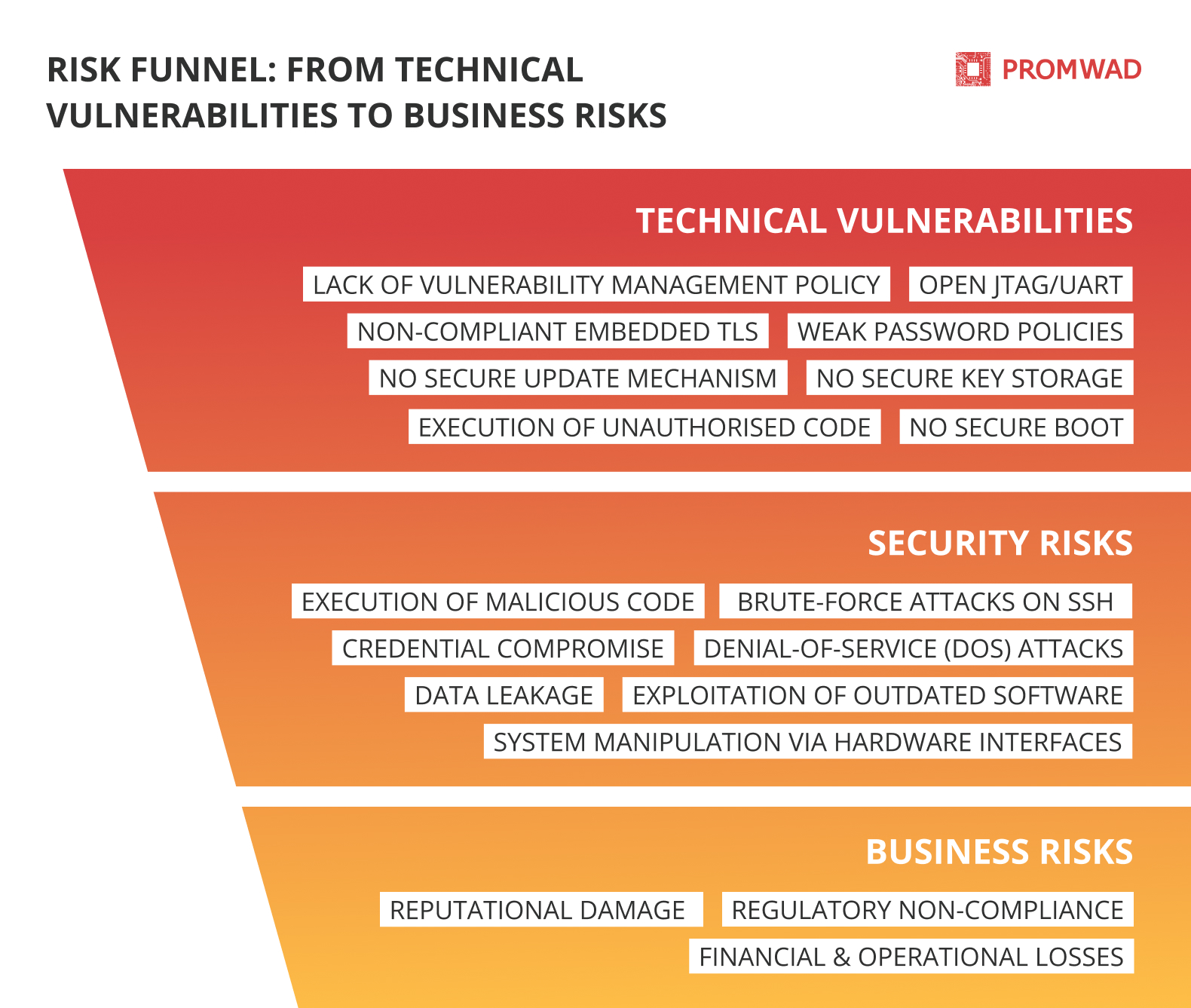
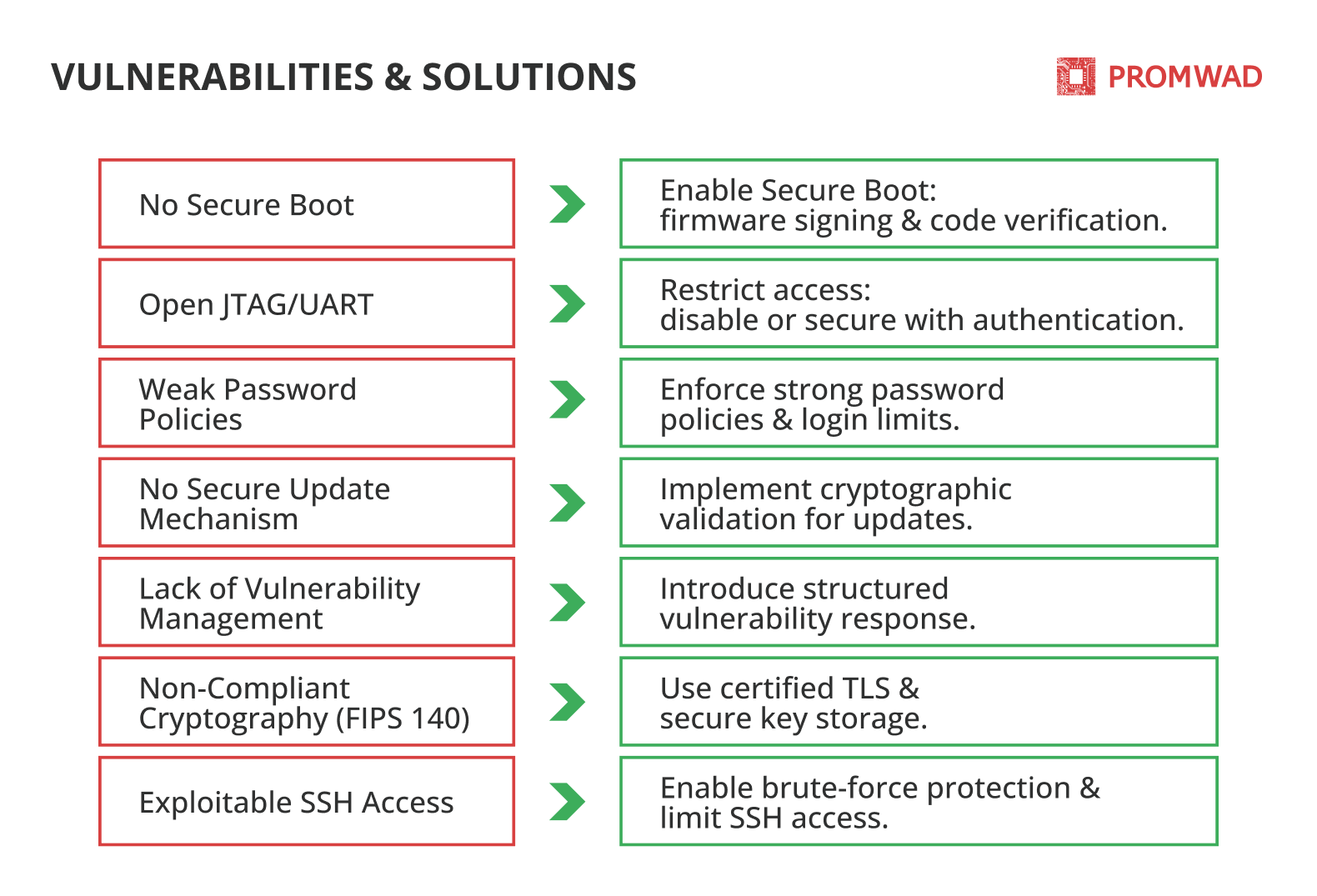
Remediation Recommendations
The identified vulnerabilities pose significant security risks, which, if left unaddressed, could lead to serious business consequences, including regulatory non-compliance, financial losses, and reputational damage. To mitigate these risks, we proposed the following measures:
- Implement Secure Boot: enable firmware signing and block unauthorised code execution.
- Restrict access to JTAG/UART: disable or protect hardware interfaces using authentication or hardware protection mechanisms.
- Adopt certified cryptography (FIPS 140): Replace embedded TLS with a FIPS 140-certified library and implement secure key storage.
- Enhance brute-force protection: enforce restrictions on login attempts and enforce strong password policies.
- Implement a secure firmware update mechanism: establish a secure update process with cryptographic signatures to ensure software integrity.
- Enable auditing and logging: track and record security-critical events for incident analysis and response.
- Implement multi-factor authentication (MFA): strengthen the protection of user accounts with an additional layer of security.
Business Value
By addressing identified security vulnerabilities, the client will improve the cyber resilience of their industrial equipment and ensure compliance with international security standards.
Compliance with the recommendations will reduce the likelihood of unauthorised access, data leakage and system manipulation.
In the long term, enhanced security helps customers meet regulatory requirements, avoid financial losses caused by security breaches, and build customer trust by providing a safer and more reliable product.
More of What We Do for Сybersecurity
- Cybersecurity Design and Development: explore the full range of services we provide in the area of cyber security
- Cybersecurity in Action: Explore our research: top embedded device threats and their impact on daily life and work.
- Malware Analysis with Automatic File Scanning: explore our malware detection automation project.