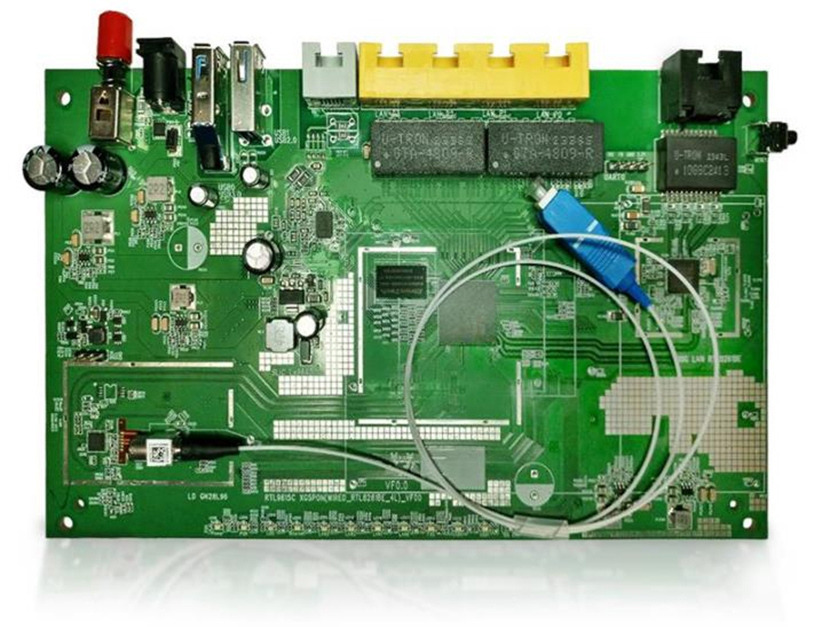
Hardware Review
We start at the board. Our hardware engineers review the architecture, identify exposed and debug interfaces, and assess physical access risks that affect the device's trust assumptions.
Typical hardware review activities:
- Review of schematics, PCB layout, and reference design adherence
- Inventory of debug interfaces such as JTAG, SWD, UART, and unused test points
- Assessment of storage, memory protection, and access to non-volatile assets
- Evaluation of secure element, TPM (platform crypto module)
- Review of platform features that may expand the attack surface
- Physical access risk assessment — tamper paths, and externally accessible signals
Outcome: a clear picture of which hardware-level conditions either enable or contain higher-layer attacks.