Development of the device for trusted session
Client
A developer and manufacturer of network security solutions. The company's solutions for building virtual private networks (VPN) provide protection for firewall interactions, wireless and multiservice networks, as well as ensure the security of remote and mobile users.
Challenge
Develop and prepare for launching into production a custom trusted computing module (TCM), which is a USB device designed to start a secure session.
The TCM should perform the following functions:
- access to a cryptographic controller operating according to ISO-7816-3;
- access to the data medium via the USB Mass Storage Interface;
- control of access to the sections on the data medium depending on the password received;
- the possibility of booting IBM PC-compatible computers from the device;
- the speed of data transfer over USB equals that of flash drives by global vendors.
It is necessary to develop a library to provide the API programmer with control of the device via USB CCID in Linux. It is also necessary to develop a software package executed on the controller and the PC, which would perform post-production testing and startup initialization of the device, involving the creation of passwords and rights, as well as the writing of operating system images to the device.
Solution
1. Hardware development
The software was based on the AT91LIB library by Atmel. The solution was designed using an ARM Cortex M3 chip.
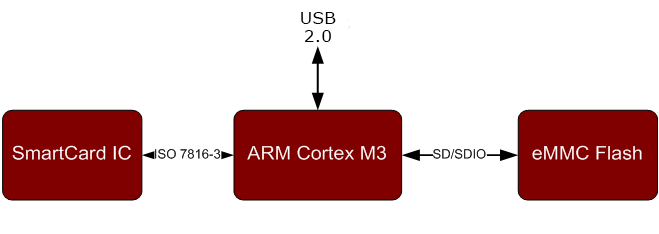
Fig.1. Structural diagram of the device
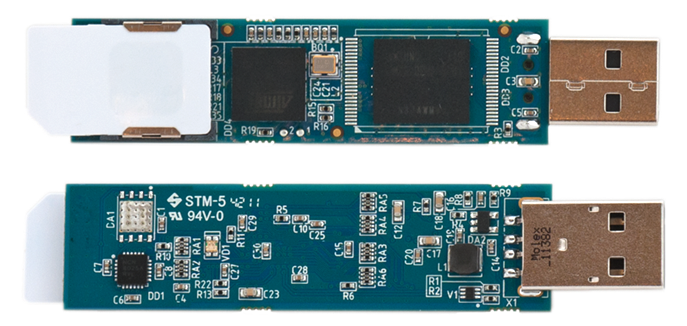
Fig.2. A hardware platform of the device
2. Software developmet
Considering the customer’s requirements, we developed the following software architecture:
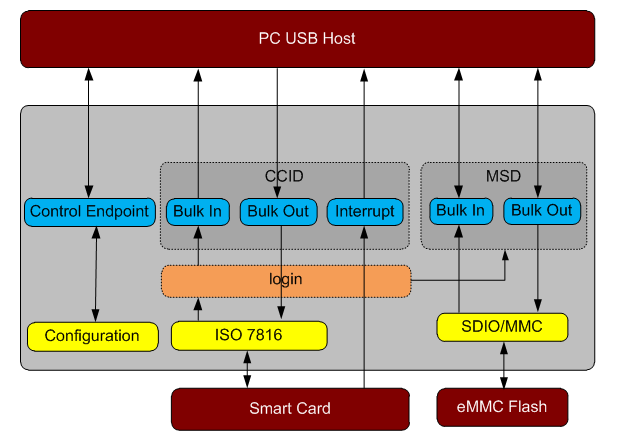
Fig.3. Software architecture
Major software modules:
- USB CCID provides access to a smart card (smart chip) through the ISO7816 interface.
- USB MSD provides access to the eMMC Flash content according to the user’s rights authorised through the USB CCID.
- Login checks the responses of the smart card through the ISO7816 interface and based on the response, issues the right of access to data in the MSD infrastructure.
The device's initialisation involved the use of the Debian 6.0 operating system, as well as the usblib and libsysfs libraries. Three libraries were created using these tools:
- libinitsbs provides the functions of authorisation and writing data to the device.
- libsbs provides the communication functions with a smart card (reset, creating a file system, adding a user, user authorisation, deleting a user, blocking a user, etc.).
- the libsysfsdev library.
Business Value
- The device operating principles are based on a fundamentally new technology for building a trusted session environment. It eliminates the costly and difficult to use security packages such as security suite, NAC, DLP, and others.
- Data on the device is protected by a crypto chip (smart card): two-factor authentication, cryptographic protection of data and traffic.
- The possibility of booting an operating system from the device.









